Cover your bases
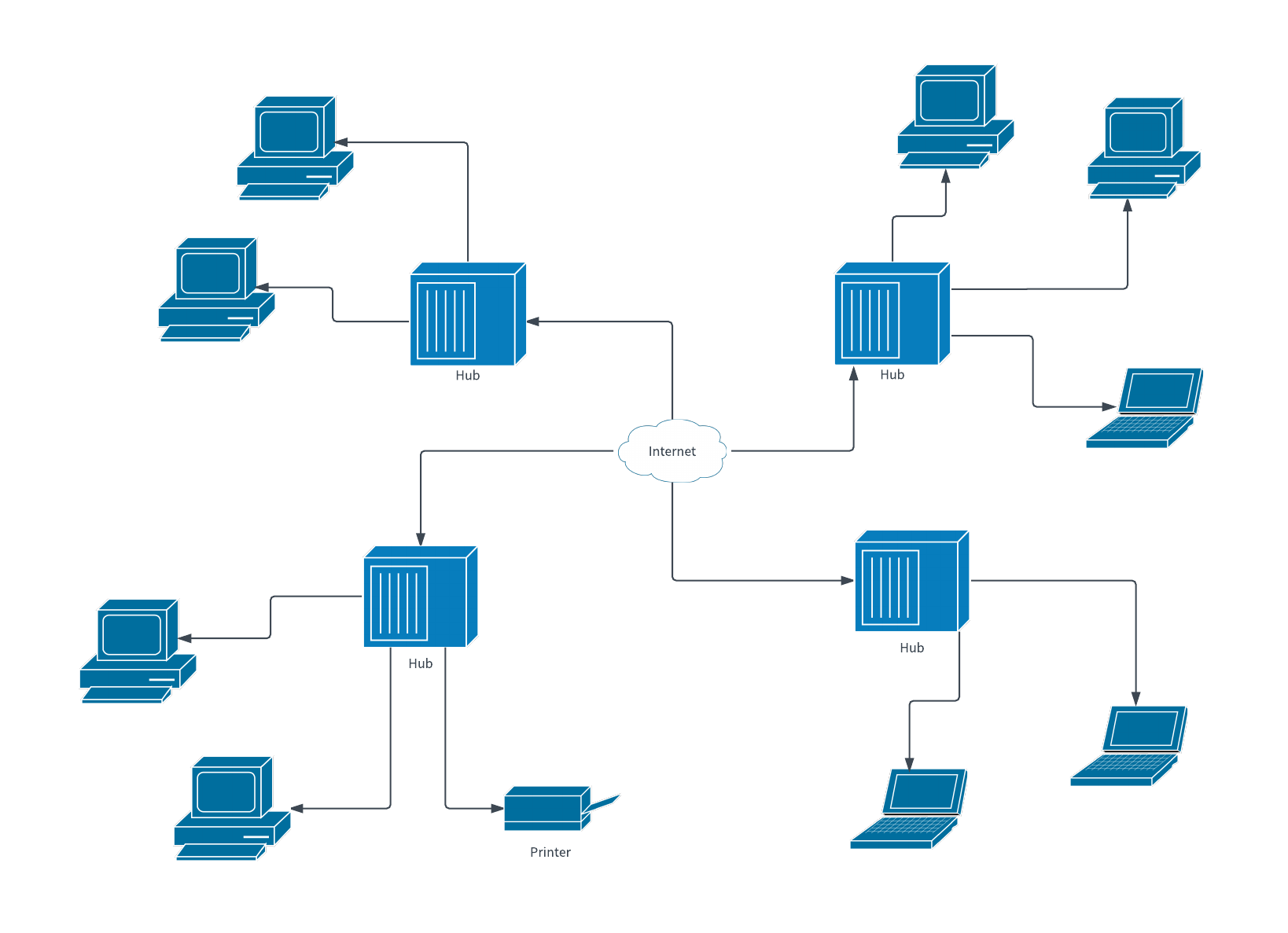
When it comes to PCI DSS compliance, you may need to create different types of network diagrams to meet compliance requirements. Some diagrams show the network at a high level, while others focus on one area or aspect of a network. Just like a map of a city, you can zoom in on a “neighborhood” to show and represent even more device and network interaction.
In the Executive Summary of a PCI Report on Compliance (ROC), businesses are required to provide (1) a general network diagram, (2) a detailed network diagram with information like encryption strength, network cards, ports, connection types, and subnets, and (3) a card data flow diagram. Below are the details you need to include in your diagrams.
A detailed network map and a general network diagram work together to show both a high-level view and a more detailed description of your network. The detailed diagram will include more information, and the general diagram will provide a cleaner layout of just the essential framework. Between the two, you need to cover the following:
- A representation of all connections in and out of the network
- All network devices in use within the cardholder data network (routers, firewalls, switches, etc.)
- All computers attached to the card network. Multiple identical systems can be represented as a group if appropriately noted
- Remote access/admin connections (VPN concentrators, SSH, modems, etc.)
- Wireless networks if installed
- Connections to any external companies
- Any modems in use
- IP addresses
- VLANs in use
A card data flow diagram needs to contain the following:
- A description of how the credit card information moves through the network, including:
- To which systems the data is passed or stored for any time
- Through which network devices the data passes
- Which port and protocols are used to pass the data to each location
- Which, if any, encryption algorithms are in use and when
- Which data is stored, where, and for how long (cardholder info, card and CVV numbers, expiration dates)
- All inbound sources of credit card information to the network
- All outbound flows of credit card data (e.g., to a payment processor, data storage companies, marketing, etc.)
It’s also important that you keep current copies of all three types of network diagrams on file. Not only is it required for PCI compliance, but it is also a key data security practice. If your company deals with protected, sensitive, classified, secret, or top-secret information, these diagrams will serve as references. They can help you recall where any critical data originates, is stored, transmitted, or received within the network—so as to ensure data confidentiality, integrity, and availability.
Use the right tools
While network diagram software and tools are not required to become PCI compliant, using these tools can save time and effort. Many people incorporate diagramming software to make their mapping easier and more organized.
Put your diagram to the test
If you want to know how accurate a network diagram is, take it to a network engineer and ask them to recreate it on a network simulator like GNS3 and then compare it to the live configuration. GNS3 and other tools allow you to upload virtual machines as network appliances for study and testing purposes.
When diagramming, your overall goal should be to balance thoroughness with clarity. When in doubt, get specific. People often forget to show details like cable types, encryption strength, wireless networks, version number, last-changed date, etc.
The top three problems we see with network diagrams are:
- They don’t contain enough detail for an assessor to determine what is or isn’t in scope for an audit.
- They don’t use industry-standard icons.
- They contain outdated information and are therefore inaccurate.
If your company is facing a PCI audit or compliance assessment, follow the suggestions and reminders above and create your detailed, thorough, and descriptive network diagrams correctly the first time.